| Protocol | Port |
|---|---|
| FTP (File Transfer Protocol) | 21 |
| SSH (Secure Shell) | 22 |
| Telnet | 23 |
| SMTP (Simple Mail Transfer Protocol) | 25 |
| HTTP (Hypertext Transfer Protocol) | 80 |
| HTTPS (Hypertext Transfer Protocol Secure) | 443 |
| POP3 (Post Office Protocol version 3) | 110 |
| IMAP (Internet Message Access Protocol) | 143 |
| RDP (Remote Desktop Protocol) | 3389 |
| SMB (Server Message Block) | 445 |
| FTPS (FTP over SSL/TLS) | 990 |
| MySQL | 3306 |
| Protocol | Port |
|---|---|
| DHCP (Dynamic Host Configuration Protocol) | 67, 68 |
| SNMP (Simple Network Management Protocol) | 161 |
| NTP (Network Time Protocol) | 123 |
| TFTP (Trivial File Transfer Protocol) | 69 |
| Protocol | Port |
|---|---|
| DNS (Domain Name System) | 53 |
| LDAP (Lightweight Directory Access Protocol) | 389 |
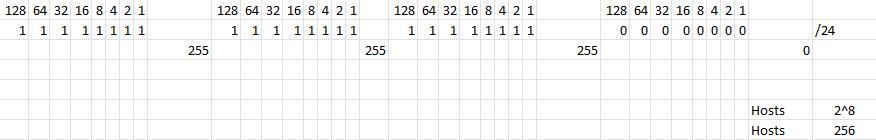
| Original Network | 192.168.0.0/24 |
|---|---|
| Subnet Mask | 255.255.255.0 |
| Subnet | Network Range | CIDR Notation |
|---|---|---|
| 1 | 192.168.0.0 - 192.168.0.63 | 192.168.0.0/26 |
| 2 | 192.168.0.64 - 192.168.0.127 | 192.168.0.64/26 |
| 3 | 192.168.0.128 - 192.168.0.191 | 192.168.0.128/26 |
| 4 | 192.168.0.192 - 192.168.0.255 | 192.168.0.192/26 |

Source: The Cyber Mentor
Source: The Cyber Mentor
